Designing for Crisis ResPonse
Alert configuration for 100,000+ security analysts monitoring active threats
Role
Senior Product Designer
/
Company
Dataminr
/
Industry
Real-time Security Intelligence
/
Duration
3 Months
/
Year
2022
Overview
(00)
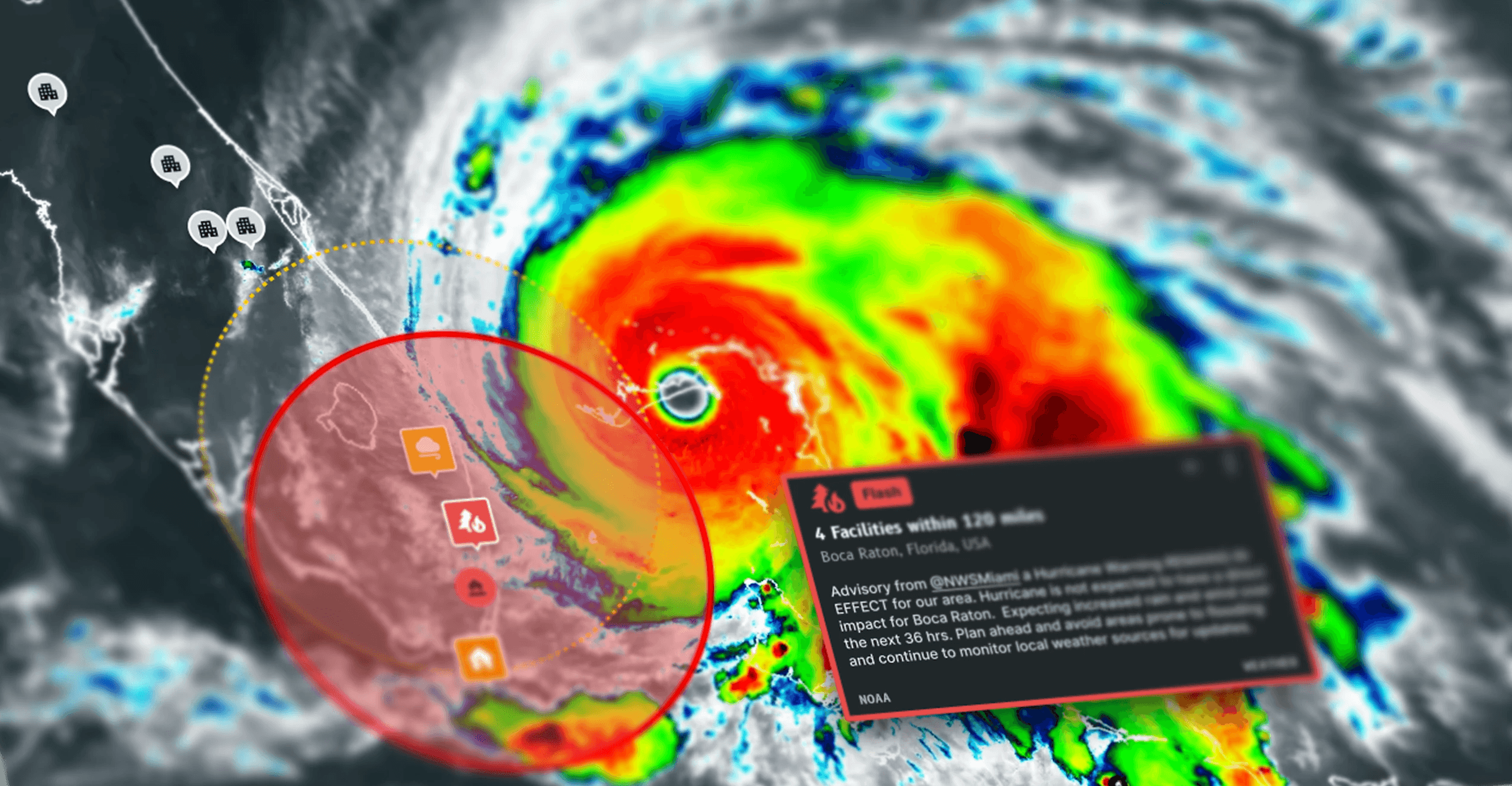
Security analysts use Dataminr to monitor for emerging risks. When a threat arises, security teams need to act fast.
A critical missed alert endangered lives and threatened key customer relationships. Rigid radius settings forced all alert types to use the same geographic coverage—creating noise and missed threats.
My research defined the problem: customers assess risk by proximity to assets, not radius circles. Corporate headquarters needs instant alerts for nearby shootings (0.5 mi) but broader coverage for severe weather (25 mi)—same asset, different threat proximity requirements. This insight shaped product direction during a post-acquisition debate and avoided nearly 2 years of wasted development.
My solution delivers critical information when security teams need it most.
Understanding the Problem
(01)
A single radius applied to all alert topics caused noise and missed threats

Individual Analysts
Same location needed different radius settings per threat type (headquarters: tight for crime, wide for weather).
Workaround: Duplicated locations into multiple folders (HQ-Traffic, HQ-Weather, HQ-Crime)
Risk: 50% of locations were duplicates. Analysts risked drowning in noise or missing critical warnings.
Security Team Managers
Configuring 300-20,000 accounts took 3-4 hours weekly and managers couldn't predict how alert rules would filter content
Workaround: 30% maintained external assignment spreadsheets
Risk: One misconfiguration deployed to thousands of analysts could cause teams to miss critical warnings.
Business impact: Contract renewals stalled and threatened churn.
Discovery
(02)
I interviewed analysts across industries and 8 enterprise managers (managing 50-5,000+ accounts).
Alert urgency depends on asset type, event type, and proximity.
All users prioritized knowing what would happen over speed.
Each location and threat type requires different settings.
Acquisition Integration
Mid-project, Dataminr acquired a third party mapping platform. Their product lead argued we move radius settings from assets to topics (event-centric approach validated with banking users).
My response:
I pushed the team to stop thinking about radius (circles on a map) and start thinking about proximity (relationship between threat and asset). Two terms that sound the same but have fundamentally different implications: radius is geometric, proximity is contextual.
This reframe shifted the debate from "how big should the circle be?" to "what threats matter to this specific asset?"
Presented to Director of Product with research evidence showing the event-centric approach would create the same proximity problem and an engineering spike showing 18-24 months of migration work with no clear benefit. Leadership agreed to build on our existing asset-centric paradigm, avoiding nearly 2 years of wasted development.
Acquisition Integration
Mid-project, Dataminr acquired a third party mapping platform. Their product lead argued we move radius settings from assets to topics (event-centric approach validated with banking users).
My response:
I pushed the team to stop thinking about radius (circles on a map) and start thinking about proximity (relationship between threat and asset). Two terms that sound the same but have fundamentally different implications: radius is geometric, proximity is contextual.
This reframe shifted the debate from "how big should the circle be?" to "what threats matter to this specific asset?"
Presented to Director of Product with research evidence showing the event-centric approach would create the same proximity problem and an engineering spike showing 18-24 months of migration work with no clear benefit. Leadership agreed to build on our existing asset-centric paradigm, avoiding nearly 2 years of wasted development.
Solution
(04)
Per-list customization for specific event types
List-level configuration for granular control across multiple locations
Expanded from cramped modal to full-screen design based on user feedback
Smart defaults: step one filters step two, changes save automatically
Advanced settings accessible for power users, optional for standard workflows
85% of analysts rely on the recommended values, while power users can access advanced controls when needed.
Per-location overrides for power users with unique requirements
85% of analysts rely on the recommended values, while power users access advanced controls when needed.


Defaults set during onboarding using industry and monitoring needs
Default radius values defined during customer onboarding are the foundation to improved alerting scope.
Default settings address the company monitoring needs, opening the door to a scalable settings solution.
The system monitors radius changes across alert lists to train recommendation models.
Impact & Outcomes
(05)
I designed a solution that provides quick setup and customization to address risk assessment needs and varying experience levels.
Individual analysts: 20% reduction in alert noise enabling faster response times during active crises, 50% fewer duplicate workarounds
Enterprise teams: 65% reduction in configuration time (3-4 hours → 1-1.5 hours weekly), 90% elimination of quarterly resets, became RFP differentiator for 10,000+ accounts
Platform-wide: Scaled these proximity settings to 100,000+ security analysts through enterprise verification workflows (see full enterprise case study).
Support tickets dropped 45% while adoption increased 40%. Patterns deployed across 3+ product interfaces.


Designing for Crisis ResPonse
Alert configuration for 100,000+ security analysts monitoring active threats
Role
Senior Product Designer
/
Company
Dataminr
/
Industry
Real-time Security Intelligence
/
Duration
3 Months
/
Year
2022
Designing for Crisis ResPonse
Alert configuration for 100,000+ security analysts monitoring active threats
Role
Senior Product Designer
/
Company
Dataminr
/
Industry
Real-time Security Intelligence
/
Duration
3 Months
/
Year
2022


Precision Alert Monitoring
How Smart Defaults Reduced Alert Noise by 20%
Role
Product Design
/
Company
Dataminr
/
Industry
Real-time Security Intelligence
/
Duration
3 Months
/
Year
2022
Precision Alert Monitoring
How Smart Defaults Reduced Alert Noise by 20%
Role
Product Design
Company
Dataminr
Industry
Real-time Security Intelligence
Duration
3 Months
Year
2022
Overview
(00)
Security analysts use Dataminr to monitor for emerging risks. When a threat arises, security teams need to act fast.
A critical missed alert endangered lives and threatened key customer relationships. Rigid radius settings forced all alert types to use the same geographic coverage—creating noise and missed threats.
My research defined the problem: customers assess risk by proximity to assets, not radius circles. This insight shaped product direction during a post-acquisition debate.
My solution delivers critical information when security teams need it most.
Understanding the Problem
(01)


Too wide = overwhelming noise. Too narrow = missed threats.
Customers duplicated location groups as workarounds
Result: Critical missed alert, churn threats from key accounts
A single radius applied to all alert topics caused noise and missed threats
Individual Analysts
Same location needed different radius settings per threat type (headquarters: tight for crime, wide for weather).
Workaround: Duplicated locations into multiple folders (HQ-Traffic, HQ-Weather, HQ-Crime)
Risk: 50% of locations were duplicates. Analysts risked drowning in noise or missing critical warnings.
Security Team Managers
Configuring 300-20,000 accounts took 3-4 hours weekly and managers couldn't predict how alert rules would filter content
Workaround: 30% maintained external assignment spreadsheets
Risk: One misconfiguration deployed to thousands of analysts could cause teams to miss critical warnings.
Business impact: Contract renewals stalled and threatened churn.
Solution
(04)
Per-list customization for specific event types
Expanded from cramped modal to full-screen design based on user feedback
Smart defaults: step one filters step two, changes save automatically
Advanced settings accessible for power users, optional for standard workflows
85% of analysts rely on the recommended values, while power users can access advanced controls when needed.




Defaults set during onboarding using industry and monitoring needs
Default radius values defined during customer onboarding are the foundation to improved alerting scope.
Default settings address the company monitoring needs, opening the door to a scalable settings solution.
The system monitors radius changes across alert lists to train recommendation models.
Analysts configure alerts the way they think about threats—not the way the system was built
Impact & Outcomes
(05)
Individual analysts: 20% reduction in alert noise enabling faster response times during active crises, 50% fewer duplicate workarounds
Enterprise teams: 65% reduction in configuration time (3-4 hours → 1-1.5 hours weekly), 90% elimination of quarterly resets, became RFP differentiator for 10,000+ accounts
Platform-wide: Scaled these proximity settings to 100,000+ security analysts through enterprise verification workflows (see full enterprise case study).
Support tickets dropped 45% while adoption increased 40%. Patterns deployed across 3+ product interfaces.
I designed a solution that provides quick setup and customization to address risk assessment needs and varying experience levels.
Discovery
(02)
I interviewed analysts across industries and 8 enterprise managers (managing 50-5,000+ accounts).
Alert urgency depends on asset type, event type, and proximity.
All users prioritized knowing what would happen over speed.
Each location and threat type requires different settings.
Analysts configure alerts the way they think about threats, not the way the system was built
Acquisition Integration
Mid-project, Dataminr acquired a third party mapping platform. Their product lead argued we move radius settings from assets to topics (event-centric approach validated with banking users).
My response:
I pushed the team to stop thinking about radius (circles on a map) and start thinking about proximity (relationship between threat and asset). Two terms that sound the same but have fundamentally different implications: radius is geometric, proximity is contextual.
This reframe shifted the debate from "how big should the circle be?" to "what threats matter to this specific asset?"
Presented to Director of Product with research evidence showing the event-centric approach would create the same proximity problem and an engineering spike showing 18-24 months of migration work with no clear benefit. Leadership agreed to build on our existing asset-centric paradigm, avoiding nearly 2 years of wasted development.
Overview
(00)
Security analysts use Dataminr to monitor for emerging risks. When a threat arises, security teams need to act fast.
A critical missed alert endangered lives and threatened key customer relationships. Rigid radius settings forced all alert types to use the same geographic coverage—creating noise and missed threats.
My research defined the problem: customers assess risk by proximity to assets, not radius circles. This insight shaped product direction during a post-acquisition debate.
My solution delivers critical information when security teams need it most.
Understanding the Problem
(01)
A single radius applied to all alert topics caused noise and missed threats
Too wide = overwhelming noise. Too narrow = missed threats.
Customers duplicated location groups as workarounds
Result: Critical missed alert, churn threats from key accounts


Individual Analysts
Same location needed different radius settings per threat type (headquarters: tight for crime, wide for weather).
Workaround: Duplicated locations into multiple folders (HQ-Traffic, HQ-Weather, HQ-Crime)
Risk: 50% of locations were duplicates. Analysts risked drowning in noise or missing critical warnings.
Security Team Managers
Configuring 300-20,000 accounts took 3-4 hours weekly and managers couldn't predict how alert rules would filter content
Workaround: 30% maintained external assignment spreadsheets
Risk: One misconfiguration deployed to thousands of analysts could cause teams to miss critical warnings.
Business impact: Contract renewals stalled and threatened churn.
Solution
(04)
Per-list customization for specific event types
Expanded from cramped modal to full-screen design based on user feedback
Smart defaults: step one filters step two, changes save automatically
Advanced settings accessible for power users, optional for standard workflows
85% of analysts rely on the recommended values, while power users can access advanced controls when needed.




Defaults set during onboarding using industry and monitoring needs
Default radius values defined during customer onboarding are the foundation to improved alerting scope.
Default settings address the company monitoring needs, opening the door to a scalable settings solution.
The system monitors radius changes across alert lists to train recommendation models.
Impact & Outcomes
(05)
I designed a solution that provides quick setup and customization to address risk assessment needs and varying experience levels.
Individual analysts: 20% reduction in alert noise enabling faster response times during active crises, 50% fewer duplicate workarounds
Enterprise teams: 65% reduction in configuration time (3-4 hours → 1-1.5 hours weekly), 90% elimination of quarterly resets, became RFP differentiator for 10,000+ accounts
Platform-wide: Scaled these proximity settings to 100,000+ security analysts through enterprise verification workflows (see full enterprise case study).
Support tickets dropped 45% while adoption increased 40%. Patterns deployed across 3+ product interfaces.
Discovery
(02)
I interviewed analysts across industries and 8 enterprise managers (managing 50-5,000+ accounts).
Alert urgency depends on asset type, event type, and proximity.
All users prioritized knowing what would happen over speed.
Each location and threat type requires different settings.
Analysts configure alerts the way they think about threats, not the way the system was built
Acquisition Integration
Mid-project, Dataminr acquired a third party mapping platform. Their product lead argued we move radius settings from assets to topics (event-centric approach validated with banking users).
My response:
I pushed the team to stop thinking about radius (circles on a map) and start thinking about proximity (relationship between threat and asset). Two terms that sound the same but have fundamentally different implications: radius is geometric, proximity is contextual.
This reframe shifted the debate from "how big should the circle be?" to "what threats matter to this specific asset?"
Presented to Director of Product with research evidence showing the event-centric approach would create the same proximity problem and an engineering spike showing 18-24 months of migration work with no clear benefit. Leadership agreed to build on our existing asset-centric paradigm, avoiding nearly 2 years of wasted development.